Why non-core systems deserve first-class infrastructure
Systems that don’t belong inside the core still require dedicated, isolated infrastructure with clear accountability, predictable performance, and audit-ready documentation.
—
Regional banks and credit unions increasingly rely on systems that operate outside their core banking platforms—including customer-facing digital experiences, vendor integrations, analytics tools, and security systems.
While these systems are often labeled “non-core,” their impact on customer trust, regulatory posture, and operational risk is significant.
This brief outlines a practical, examiner-safe framework for determining where systems should live, how they should be governed, and how institutions can innovate without increasing risk.
The premise: systems that don’t belong inside the core still require dedicated, isolated infrastructure with clear accountability, predictable performance, and audit-ready documentation.
The challenge institutions face
Most infrastructure decisions have historically been framed as a binary choice:
- Core systems (highly controlled, standardized)
- Everything else (often treated as lower risk)
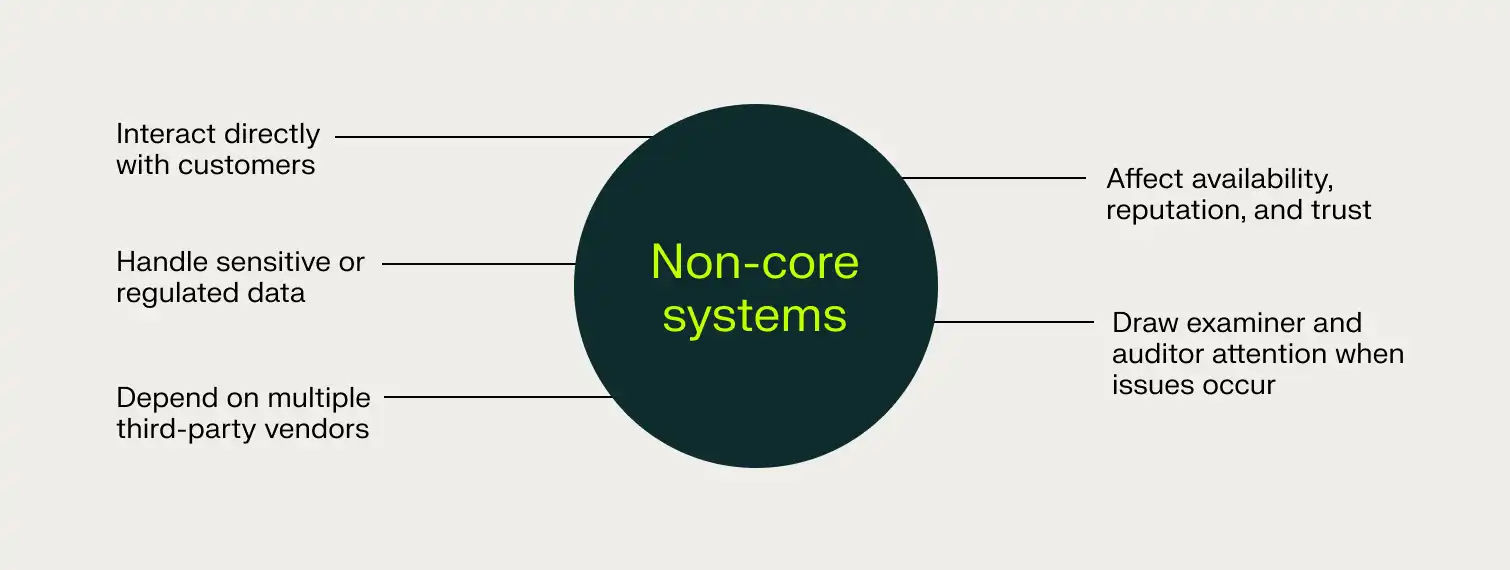
That model doesn’t reflect the current reality. Today, many non-core systems:
- Interact directly with customers
- Handle sensitive or regulated data
- Depend on multiple third-party vendors
- Affect availability, reputation, and trust
- Draw examiner and auditor attention when issues occur
The risk comes from placing these systems on infrastructure that can’t be clearly governed, examined, or defended—where performance is unpredictable, accountability is fuzzy, and failures spread farther than anticipated.
How examiners actually evaluate systems
Examiners do not assess systems based on whether they’re core or non-core. They evaluate systems based on whether the institution can clearly demonstrate:
- Risk awareness
- Appropriate controls
- Clear ownership and accountability
- Documented responsibilities
- Effective monitoring and incident response
Examiners ask:
- Why does this system live where it does?
- Who owns it?
- How is risk mitigated?
- How does it behave under pressure?
- How do you know it’s working as intended?
Infrastructure decisions that cannot answer these questions create regulatory exposure.
The role of first-class infrastructure
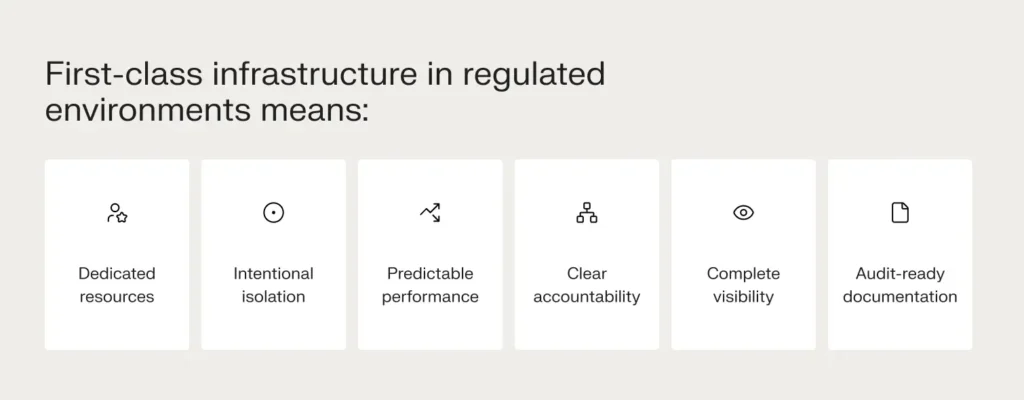
This level of rigor is standard for core platforms. Non-core, mission-critical systems require it too.
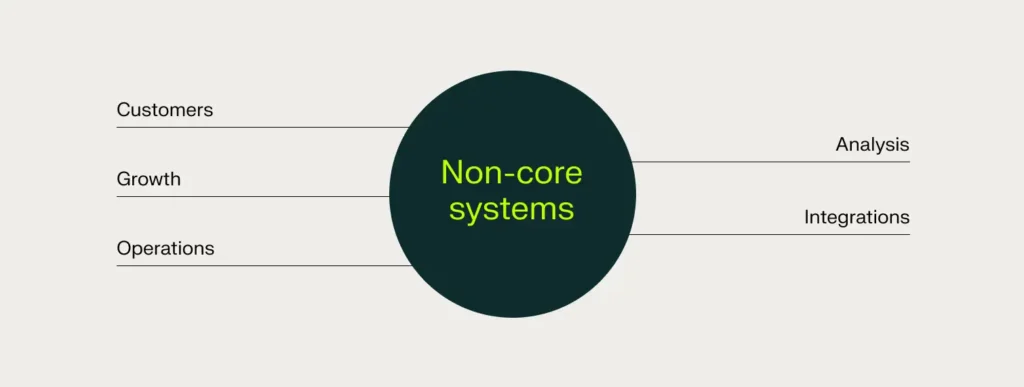
Common categories of non-core, mission-critical systems
Institutions most often see this challenge in these areas:
Customer-facing digital systems
Public websites, digital experience layers, onboarding tools, and marketing platforms are often the first systems customers interact with—and the first scrutinized when availability or security issues arise.
Vendor and integration ecosystems
Fintech vendors, middleware, APIs, and data exchanges enhance capabilities but expand the third-party risk surface when the responsibility for infrastructure isn’t clear.
Innovation and pilot environments
New tools require testing or validation outside the core. Without controlled environments, pilots can introduce risk unintentionally.
Sensitive or special-purpose workloads
Fraud analytics, digital forensics, security tooling, and regulatory reporting systems often demand heightened controls despite operating outside core processing platforms.
None of these systems typically belong in the core. All of them require infrastructure with clear ownership and predictable performance.
A common (and understandable) mistake
When faced with these pressures, institutions often default to one of two approaches:
- Forcing non-core systems into the core platform. This slows innovation and stretches core platforms beyond their intended purpose.
- Placing non-core systems on generic or shared infrastructure. This can create hidden risks that surface during incidents, audits, or exams.
Neither approach reliably produces clear, defensible answers to examiner questions. Shared infrastructure makes it harder to demonstrate predictable behavior, trace accountability, or explain what happened when questions pop up.
Introducing an intentional architecture model
A more durable approach is intentional architecture—placing systems based on function, risk, and control requirements rather than convenience.
This model recognizes three realities:
- Core platforms exist to protect stability and standardization
- Not all important systems belong inside the core
- Non-core systems can still meet the same standards of rigor and accountability
What this enables for the institution
When non-core systems are supported by first-class, dedicated, isolated infrastructure:
- Security teams gain clearer responsibility boundaries and documented controls
- Compliance teams gain audit-ready documentation aligned to regulatory frameworks
- IT teams gain predictable performance and fewer emergency escalations
- Executives gain confidence that growth doesn’t create hidden risk or cost uncertainty
- Boards gain clarity and can trust that infrastructure decisions are solid
A common, defensible narrative emerges: ‘We deliberately separate core and non-core systems, while applying appropriate controls to both.
The role of Nexcess
Nexcess supports this model by providing dedicated, compliance-ready infrastructure designed for non-core, mission-critical systems in regulated environments.
Our focus:
- Dedicated, isolated environments that eliminate shared risk and performance variability
- Clear responsibility models with no ambiguity about who owns what
- Predictable performance that doesn’t depend on other workloads
- Audit-ready documentation aligned to regulatory frameworks
- Expert support from teams who understand regulated environments and compliance realities
We don’t replace core banking platforms. We provide the infrastructure and expertise that let institutions run everything around the core with confidence.
The takeaway
Non-core systems influence customer trust, shape regulatory posture, and create or mitigate institutional risk.
Treating them as first-class means providing dedicated infrastructure with clear accountability, predictable performance, and complete visibility.
That’s infrastructure leaders can trust.
Table of contents
- The challenge institutions face
- How examiners actually evaluate systems
- The role of first-class infrastructure
- Common categories of non-core, mission-critical systems
- A common (and understandable) mistake
- Introducing an intentional architecture model
- What this enables for the institution
- The role of Nexcess
- The takeaway
Get hosting news and tips straight to your inbox
Join our community today.
Essential Hosting Resources to help your business stay ahead
Share this page


